Self-Encrypting Drives: A Brief Introduction and Step by Step Guide
A SED, or self-encrypting drive, is a blazon of hard drive that automatically and continuously encrypts the data in it without any user interaction. What may surprise many is that a decent potion of the drives currently in the market, including the pop Samsung 840 Pro SSD series are in fact SEDs. But since manufactures do not tout this as a major feature, it frequently gets lost in the big number of typically more important specifications.
Even one time you lot purchase, install, and beginning using one of these SED drives, the encryption is then transparent to the user that it is unlikely they would always realize the bulldoze is a SED.
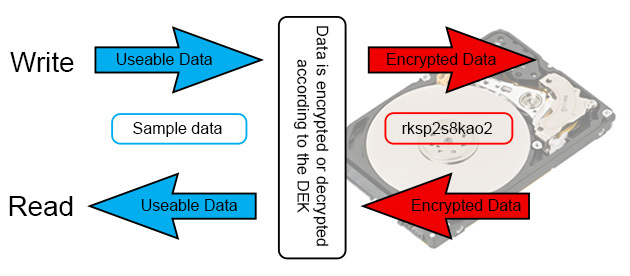
This encryption procedure is washed through the use of a unique and random Data Encryption Fundamental (DEK) which the drive uses to both encrypt and decrypt the data. Whenever data is written to the drive, it first gets encrypted according to the DEK. Similarly, whenever information is read from the drive, it first gets decrypted past the same DEK before beingness sent to the residual of the system.
Editor'southward Annotation:
Guest writer Matt Bach is the head of Puget Labs and has been office of Puget Systems, a boutique builder of gaming and workstation PCs, since the early days working in various subsets of production. This commodity was originally published on the Puget blog.
This means that all the data on the drive is encrypted at all times. One neat play tricks that tin exist done based on this is to almost instantly and completely wipe a hard bulldoze. All yous need to exercise is tell the SED to generate a new DEK and all the data on the bulldoze immediately becomes gibberish (since the key needed to decrypt the data no longer exists) and is effectively unretrievable. Then if you lot need to apace and securely wipe a drive before either redeployment or disposal, SEDs offer a quick and very secure mode to exercise so.
This act is chosen a number of different names depending on the manufacturer, although it is most often referred to equally doing a "Secure Erase".
What is SED Encryption?
While having the data encrypt and decrypt automatically on a hard drive is nifty, information technology isn't really all that useful on its own since the hard bulldoze will automatically decrypt the data on asking. However, SEDs also permit you to gear up what is called an Authentication Key (AK) which acts as a countersign that locks the bulldoze until the key is entered. If an Hallmark Fundamental is gear up, the organization will prompt for the primal when information technology showtime powers on. While the number of attempts varies by the motherboard, if you put in the incorrect countersign subsequently three or 4 attempts, the system will merely keep the drive locked and continue the boot process. If that happens, the drive becomes completely unusable until the computer is powered off and the correct key is entered.

In fact, even if you remove it from the original computer and plug it into a different computer the drive volition still require the AK to be entered in order for the drive to unlock. Nonetheless, if you you plug information technology into a system that does non support SED encryption, the bulldoze will exist unusable. Since the motherboard does not have the power to enter the Hallmark Cardinal, the bulldoze never knows to unlock itself. The result is that the bulldoze will remaining locked with no way to unlock it. Unless you move the bulldoze to a system that supports SED encryption, at that place is no way to call up the data on that drive.
According to Seagate, this method of encryption has been certified by both the NIST and CSE every bit meeting the requirements for level 2 security for cryptographic modules.
Downsides of SED encryption
When data security is a goal, information technology is essential to know the limitations and drawbacks of a sure technology. SEDs are a peachy technology, but they are no different than anything else in that they certainly take downsides. In the instance of SEDs, the main downside is that one time the drive has been unlocked, it remains so until the power to the drive has been cut. In other words, if you lot but reboot the computer or put information technology into sleep, the bulldoze remains unlocked. It is not until you completely ability off the calculator that it will once more require the Authentication Cardinal to be entered.
In other words, if your laptop is stolen and information technology was only in sleep way and so the data on the drive is completely exposed. If you take a user password set up on the Bone, a thief could even so but restart the machine, kicking into a live surround, and have near full admission to your data. In fact, even if yous take both an OS password and a BIOS password prepare, the data even so could exist accessed past moving the drive to a dissimilar reckoner without cutting the power. In laptops this would be tricky (but not impossible) but on a desktop is actually rather like shooting fish in a barrel with the right setup.
So if you do decide to use SED encryption, our biggest advice is to become into the addiction of powering off your system when it is not in utilise rather than simply putting information technology to slumber.
A second downside to SED encryption is that information technology volition only work in simple disk configurations. Yous can have multiple drives in ane system with SED encryption enabled and even utilize software RAID, just doing something like hardware-level RAID is simply not supported.
What is needed for SED encryption to work?
Something we've constitute is that total support for SED is really very poor. At that place are plenty of hard drive and SSD models that support SED encryption (although finding them can exist difficult), but full support for SED also requires a compatible motherboard.
Some features of SED (like the automated encryption and decryption of data and Secure Erase) volition piece of work regardless of the motherboard. But if you desire to use SED encryption by setting an Hallmark Primal, you need a motherboard that supports doing so.
Many laptops have the ability to use an Authentication Central without whatsoever need for a custom BIOS. Withal, they often lack the ability to set up the AK though the BIOS. Of course, this doesn't hateful that every laptop will support SED encryption, but in our experience laptops in general are much more likely to back up it than desktop or server motherboards.
While talking with Asus, Super Micro, and Samsung, we have discovered that most desktop and server motherboards do fully back up SEDs, simply the ability to use an Authentication Fundamental is expressly disabled. The reason for this appears to be that manufactures are afraid that a user may accidentally lock their hard drive and not recollect what they used for the Authentication Fundamental. So rather than gamble having an angry customer that accidentally locked their drives, they leave that specific feature of SEDs disabled. That said, we've had success with getting custom BIOS files from the manufacturer that unlocked the ability to use Authentication Keys.
Managing SED encryption passwords
On a motherboard that fully supports SED encryption, there is a chance that there is an choice in the BIOS setup to gear up, change, or remove the SED Authentication Key on your SED bulldoze. However, we have found that many motherboards that support SED do non have this adequacy built into the BIOS. In those cases, you could use software similar Winmagic to manage the SED encryption key, or you tin become through a series of steps using a Linux alive environment to manage the SED Authentication Key without the need for paid software.
You tin follow the directions from Ubuntu on how to create a LiveCD that should include everything you will need. Once your system has booted into the Linux live environment, at that place are three combinations of steps you lot must go through in order to either set, remove, or change the SED encryption password.
- No matter what you want to do, you must first locate the drive that y'all desire to manage the SED encryption password on and unfreeze it.
- Next, if yous want to change the SED encryption password or remove SED encryption entirely, you demand to disable SED encryption.
- Finally, you need to enable SED encryption with a new password if yous are either changing the SED encryption password or setting a new SED encryption countersign.
Locating and unfreezing the drive
1
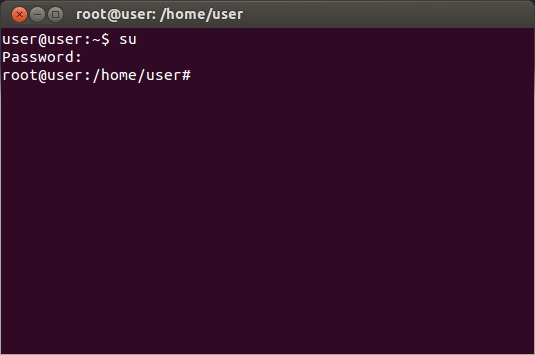
Open a terminal from the unity toolbar or with the hotkey combination "ctrl+T"

2
Enable root privileges past entering the command 'su'. You lot will be prompted for a password.
three
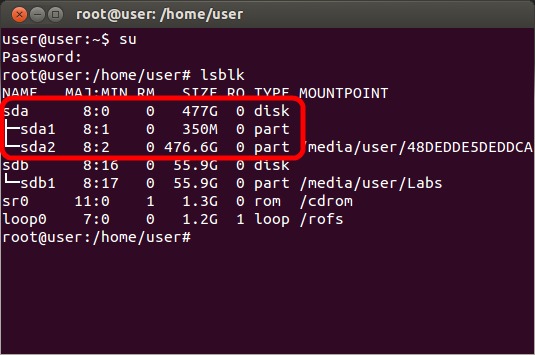
Enter the command "lsblk" which will output a list of the drives that are in the system. Locate the proper noun of the drive (sda, sdb, etc.) that y'all want to alter the encryption password or disable SED encryption on.
4
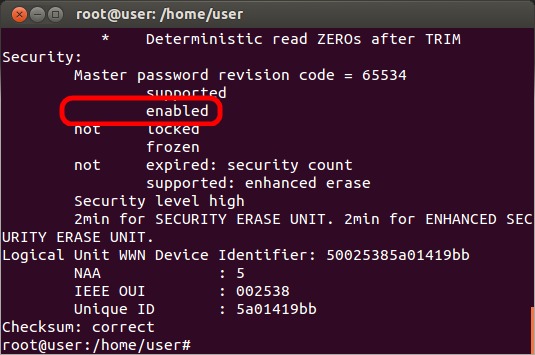
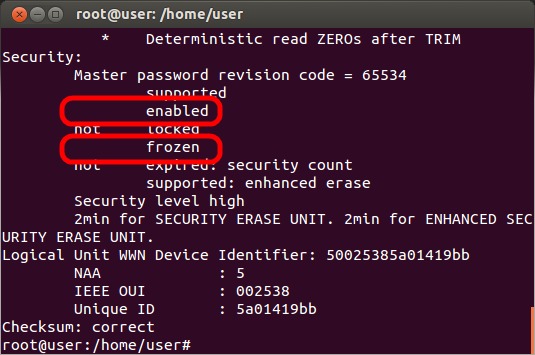
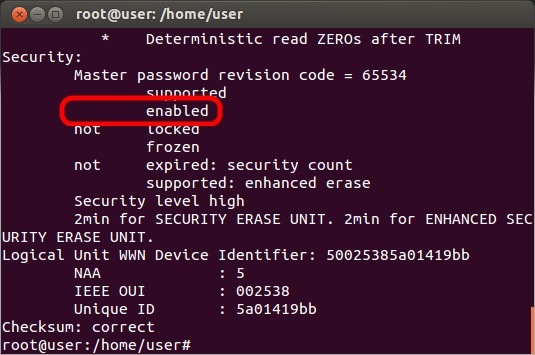
Enter the command "hdparm -I /dev/X" where X is the drive name (sda, sdb, etc.) to check the current condition of the drive. Be certain to utilize "-I" which is an uppercase i, not a one or lowercase Fifty. Cheque to make sure that there is a line that says "enabled". If that line instead says "non enabled", and so SED encryption is not currently enabled on that drive. Either SED encryption was never configured, or you are using the incorrect hard drive name (sda, sdb, etc.)
5
Typically, the drive volition be marked as frozen (indicated by a line that says "frozen") and will demand to be unfrozen before continuing. To unfreeze the drive, put the system to sleep by clicking on the gear icon at the top-correct of the screen and selecting "Suspend". Afterwards ~ten seconds, hit the power button to wake the organization upward.
half-dozen
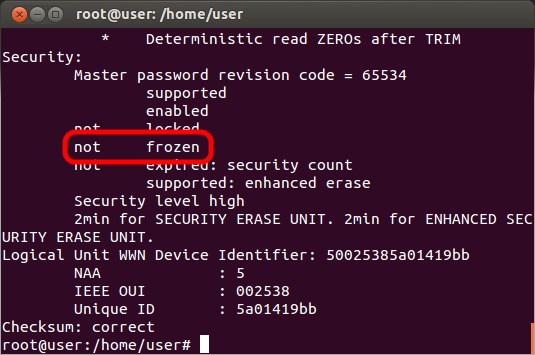
Repeat the "hdparm -I /dev/Ten" command to verify that the drive is now marked as "not frozen". If it is still frozen, yous volition demand to physically disconnect the drive for a few seconds while the arrangement is in the alive environment and then repeat the command.
Disable the current SED encryption
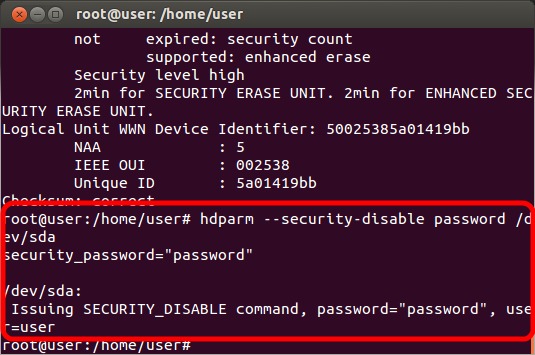
After following the steps to locate and unfreeze the drive, run the command "hdparm --security-disable Countersign /dev/X" where PASSWORD is the current SED password and X is the bulldoze proper name (sda, sdb, etc) to remove the current SED encryption. If you wish to exit SED disabled, so the process is complete. If you desire to reset SED with a new password, read on.
Enable SED encryption with a new password
1
After following the steps to locate and unfreeze the drive then to disable SED encryption, adjacent enter the control "hdparm --user-master u --security-set-laissez passer PASSWORD /dev/10" where Countersign is the password you want to use and X is the drive name (sda, sdb, etc.) to re-enable SED encryption with a new password.
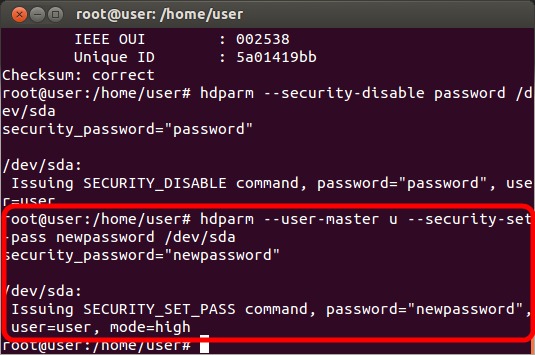
2
Enter the control "hdparm -I /dev/10" over again and look for the line "enabled" (instead of "not enabled") to ensure that SED is enabled. At this betoken you should completely power off your organization (not a standard reboot) to ensure that the SED password is set properly.
Conclusion
After working with SED encryption and seeing how well it works, we are actually very surprised at how little support information technology has on modernistic motherboards. In fact, many motherboard manufacturers actively disable SED encryption and require a custom BIOS in order to make it active. Other motherboards, nevertheless, do back up SED encryption although the ability to manage the countersign is non available from the BIOS. In those cases, you lot can still use SED encryption just you need to go though an unwieldy process involving a Linux live surround.
Overall, we accept found that SED encryption is peachy as long as you do your homework and know that it volition work on your system. Self-encrypting drives accept their downsides (largely that it simply requires the password to be entered when the machine is showtime turned on), simply it is piece of cake to employ and constructive for a very wide range of applications.
If you are interested in encrypting your information, we highly recommend checking out SED encryption before considering options like Bitlocker or other software-based encryption.
Do you employ hard drive encryption in your figurer, either SED encryption or something else? Allow us know about your experience in the comments below!
Header image via Shutterstock
Source: https://www.techspot.com/guides/869-self-encrypting-drives/
Posted by: labontecrind1971.blogspot.com


0 Response to "Self-Encrypting Drives: A Brief Introduction and Step by Step Guide"
Post a Comment